What is ZTNA? – Definition
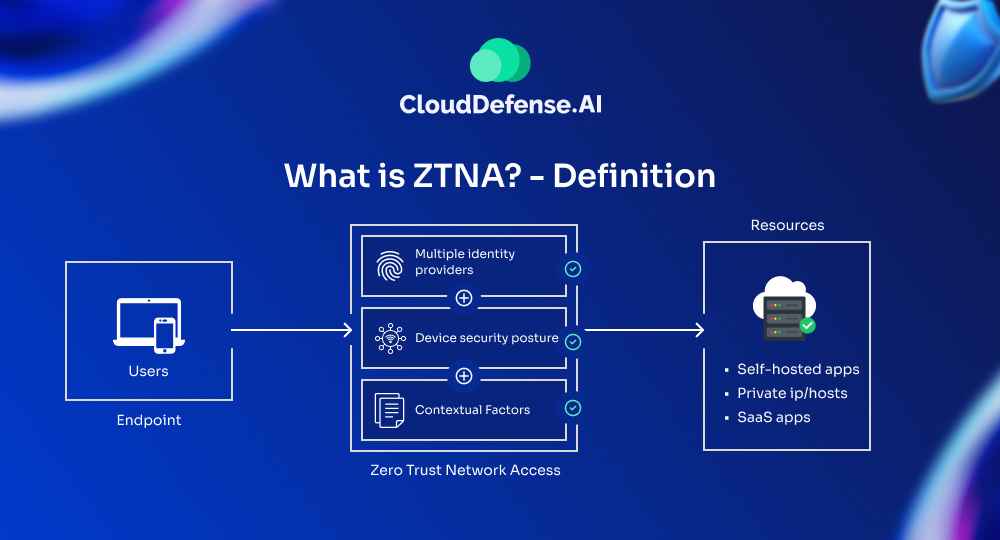
ZTNA is a security model and set of technologies that operate on the principle “never trust, always verify.” It’s based on a simple but a kind of radical idea: don’t automatically trust anyone or anything, even if they’re already inside your network. Instead, verify every single request for access, no matter where it’s coming from.
Here’s the deal: In the old days, once you were inside a company’s network, you pretty much had the run of the place. ZTNA says, “Nope, not anymore.” And, the cool thing about ZTNA is that it works whether you’re in the office, working from your favorite coffee shop, or chilling on a beach somewhere. It doesn’t care about your location – it’s all about who you are and what you’re trying to access.
Key aspects of ZTNA

- Identity-based access—Access is granted based on user identity and context, not network location.
- Least privilege access—Users are given the minimum level of access needed to perform their tasks.
- Micro-segmentation—The network is divided into small segments, limiting lateral movement if a breach occurs.
- Continuous monitoring and validation—User activities and device health are constantly monitored and re-verified.
- Multi-factor authentication (MFA)—Multiple forms of authentication are required to access resources.
- Encryption—All data, both in transit and at rest, is encrypted.
- Device access control—Only managed and compliant devices are allowed to access resources.
- Application-level access—Instead of granting access to entire network segments, ZTNA provides access to specific applications.
- Dynamic policy enforcement—Access policies are continuously updated based on risk assessments.
- Visibility and analytics—Comprehensive logging and analysis of all access attempts and user activities.
ZTNA replaces traditional VPN-based remote access solutions, offering more granular control and better security. It’s particularly well-suited for today’s distributed workforce and cloud-based environments, where the traditional network perimeter is no longer clearly defined.
How does ZTNA work?

Here’s a detailed explanation of how ZTNA functions:
Trust Nothing Approach: ZTNA starts with the assumption that no user or device should be trusted by default, even if they’re inside the network perimeter. This is a key difference from traditional security models.
Identity Verification: When a user or device tries to access a resource, ZTNA requires them to prove their identity. This typically involves multi-factor authentication (MFA), which could include something you know (like a password), something you have (like a phone), and something you are (like a fingerprint).
Device Assessment: ZTNA doesn’t just verify the user – it also checks the device they’re using. It looks at factors like whether the device has up-to-date security software, if it’s been compromised, and if it meets the organization’s security standards.
Least Privilege Access: Once identity and device are verified, ZTNA grants access based on the principle of least privilege. This means users only get access to the specific resources they need for their job, nothing more.
Continuous Monitoring: ZTNA doesn’t stop at granting access. It continually monitors the session, looking for any unusual behavior or signs of a compromise. If anything suspicious is detected, access can be immediately revoked.
Micro-segmentation: ZTNA uses micro-segmentation to divide the network into small segments. Each segment contains specific resources, and access to each segment is controlled separately. This limits the potential damage if a breach occurs.
Encryption: All traffic in a ZTNA system is encrypted, protecting data both in transit and at rest.
Application-level Access: Instead of granting access to entire network segments, ZTNA provides access to specific applications, further reducing the attack surface.
Context-based Policies: ZTNA uses context to make access decisions. This could include the user’s location, the time of day, the type of device being used, and the sensitivity of the resource being accessed.
Dynamic Policy Enforcement: Policies in ZTNA are not static. They can change based on risk levels, user behavior, and other factors.
Implementing these principles, ZTNA creates a more secure environment that’s better suited to today’s distributed workforce and cloud-based resources. It’s a significant shift from traditional perimeter-based security, offering more granular control and better protection against modern threats.
Benefits of ZTNA
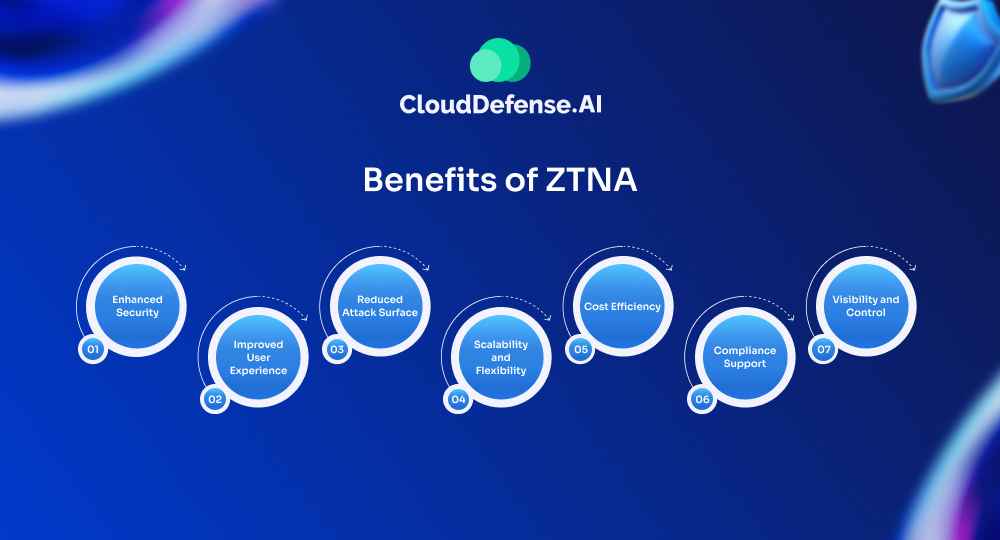
Enhanced Security
ZTNA significantly tightens things up. It verifies every access request, regardless of where it’s coming from. This means even if someone’s already inside your network, they still have to prove they should be there. It’s a game-changer for stopping the lateral movement of threats and keeping sensitive data locked down.
Improved User Experience
Despite the strict security, ZTNA can actually make life easier for users. Once set up, it provides seamless access to authorized resources—no more juggling multiple VPNs or remembering different login procedures for various systems. Users get what they need, when they need it, without jumping through hoops.
Reduced Attack Surface
By hiding resources from the public internet and only connecting users to specific applications, ZTNA shrinks your attack surface dramatically. There’s simply less for bad actors to target.
Scalability and Flexibility
ZTNA is built for the cloud era. It scales easily to accommodate growing businesses and adapts smoothly to changing work environments. Whether you’re adding new remote workers or integrating acquired companies, ZTNA flexes to fit your needs without massive overhauls.
Cost Efficiency
Over time, ZTNA can save you serious cash. It reduces the need for expensive hardware-based security solutions and simplifies your overall security infrastructure. Plus, by preventing breaches more effectively, you’re avoiding the massive costs associated with data loss and recovery.
Compliance Support
Many industries are facing stricter data protection regulations. ZTNA helps tick a lot of those compliance boxes. Its granular access controls and detailed logging make it easier to demonstrate that you’re handling sensitive data responsibly.
Visibility and Control
ZTNA gives you a clearer picture of what’s happening in your network. You can see who’s accessing what, when, and from where. This visibility is gold for spotting unusual patterns and stopping threats before they become major problems.
ZTNA vs. VPN
| Feature | ZTNA | VPN |
| Access Model | Zero Trust: Grants access to specific applications based on user, device, and application policies. | Network Access: Grants access to the entire corporate network once authenticated. |
| Security Model | Least privilege: Users only get access to what they need. | All or nothing: Users have access to all resources they are authorized for within the network. |
| Authentication | Multi-factor authentication (MFA) often used. | Often relies on username and password only. |
| Authorization | Granular control over access based on policies. | Limited control over access within the network. |
| Network Visibility | Users only see the specific application they are authorized for. | Users see the entire network layout. |
| Performance | Can be faster due to direct application access. | May experience performance impact due to encryption overhead and potential routing inefficiencies. |
| Scalability | Well-suited for cloud-based applications and hybrid workforces. | Can be complex to manage with a large number of remote users. |
| Cost | Can be more expensive than traditional VPNs, but ongoing maintenance may be lower. | Generally lower upfront cost, but ongoing maintenance can be higher. |
| Deployment | Cloud-based deployment simplifies setup and management. | Requires configuration on both user devices and network infrastructure. |
| Suitable for | Modern, cloud-based workforces with a focus on granular access control and security. | Legacy systems or scenarios where broad network access is needed. |
What is ZTNA 2.0?
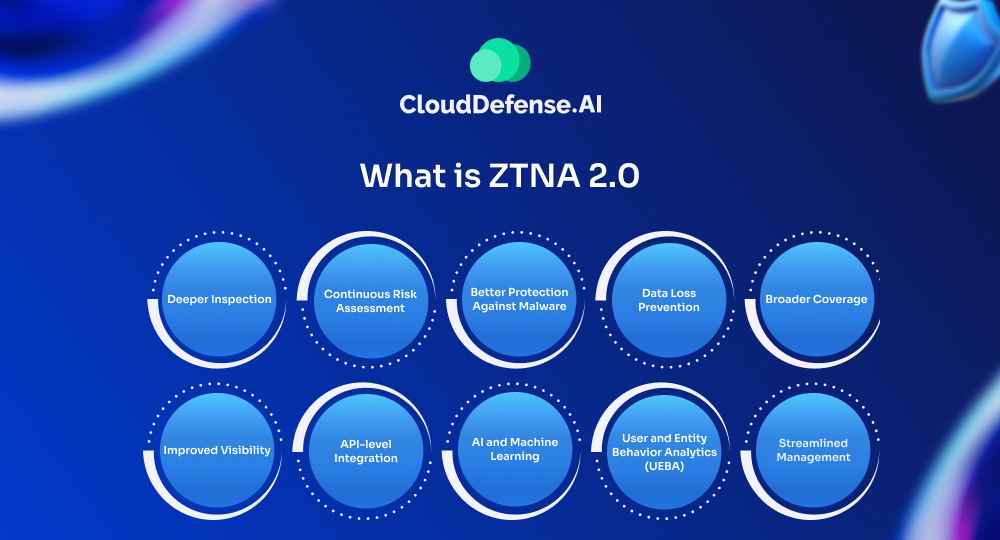
ZTNA 2.0 is an emerging concept that builds upon the foundation of Zero Trust Network Access (ZTNA). It aims to address some of the limitations of ZTNA 1.0 and further enhance security and access control in the context of remote access. Here’s what you need to know about ZTNA 2.0:
Deeper Inspection
ZTNA 2.0 goes beyond just controlling access. It inspects the content of network traffic in real-time, looking for malware, data exfiltration attempts, and other threats.
Continuous Risk Assessment
While ZTNA 1.0 does some ongoing monitoring, ZTNA 2.0 takes this further. It constantly evaluates risk based on user behavior, device health, and other factors, adjusting access privileges on the fly.
Better Protection Against Malware
ZTNA 2.0 includes advanced threat prevention capabilities. It can detect and block malware before it reaches its target, even if it’s hidden in encrypted traffic.
Data Loss Prevention
ZTNA 2.0 integrates data loss prevention (DLP) features. It can prevent sensitive data from being uploaded, downloaded, or shared inappropriately.
Broader Coverage
ZTNA 2.0 extends protection to a wider range of resources, including SaaS applications, websites, and even email.
Improved Visibility
It offers more detailed insights into user activity, application usage, and potential security risks across the entire environment.
API-level Integration
ZTNA 2.0 can integrate directly with applications at the API level, providing more granular control and better security for cloud-native apps.
AI and Machine Learning
These technologies are used more extensively in ZTNA 2.0 to detect anomalies, predict potential threats, and automate responses.
User and Entity Behavior Analytics (UEBA)
ZTNA 2.0 incorporates UEBA to detect insider threats and compromised accounts more effectively.
Streamlined Management
Despite its increased capabilities, ZTNA 2.0 aims to simplify management through automation and integration.
ZTNA 2.0 represents the next evolution of secure remote access. It offers a more secure, adaptable, and user-friendly approach to ZTNA, making it a promising solution for organizations with dynamic cloud environments and hybrid workforces.
Final Words
ZTNA represents a significant shift in how we approach network security. It’s not just a new technology but a whole new mindset. As cyber threats evolve and our work environments become more complex, ZTNA offers a more flexible, secure, and scalable solution than traditional models.
However, implementing ZTNA isn’t a simple matter of flipping a switch. It requires careful planning, user education, and often a cultural shift within organizations. But the benefits—improved security, better user experience, and more efficient operations—make it worth the effort.
As we move forward, ZTNA will likely become the norm rather than the exception. It’s time for organizations to start thinking about how they can embrace this approach to stay ahead of the curve.







