How does a Perimeter Firewall work?
Perimeter firewall operates as a barrier between an organization’s internal network and untrusted external public networks. It checks all incoming and outgoing network packets, allowing or blocking them based on security rules that were established before. The firewall analyzes packet headers to decide whether to allow the traffic. These headers contain details such as destination and source IP addresses, protocol types, and port numbers.
Types of Perimeter Firewalls
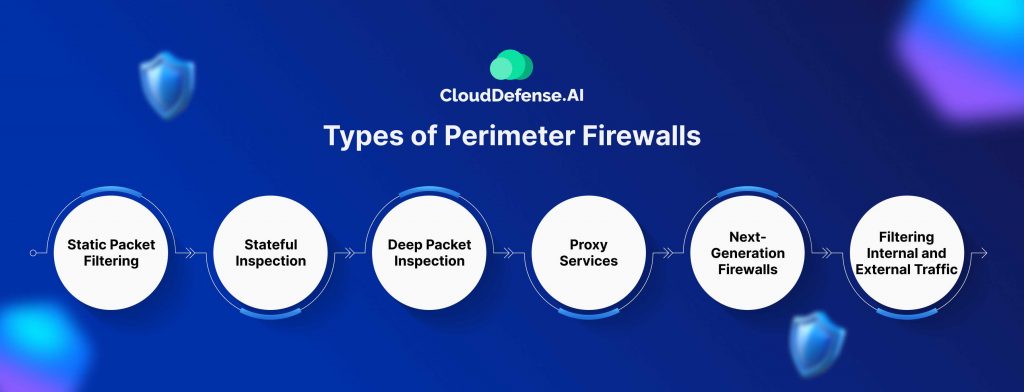
Here are a few different types of perimeter firewalls and an overview of how they operate.
1. Static Packet Filtering
Static packet filtering is one method used by perimeter firewalls. It filters traffic based on the packet header information. If the header contains data from an unwanted source, the firewall can block the packet, preventing access to banned websites or malicious sources.
2. Stateful Inspection
Stateful inspection, also known as dynamic packet filtering, tracks the state of active network connections. It maintains a record of outgoing traffic and only allows incoming traffic if it matches a previous request. This prevents unauthorized access attempts to the network and protects against IP spoofing and network scanning.
3. Deep Packet Inspection
Latest perimeter firewalls often employ deep packet inspection, or DPI, to examine packet payloads for identified threats or irregularities. DPI is vital for recognizing and minimizing complex threats fundamental security checks might miss.
4. Proxy Services
Some perimeter firewalls use proxy services, acting as intermediaries between users and the internet. The proxy server establishes separate connections between the internal network and external networks, preventing direct packet transfers and enhancing privacy by concealing users’ IP addresses.
5. Next-Generation Firewalls
Next-generation firewalls, or NGFWs, combine the features of packet filtering and stateful firewalls with advanced security capabilities. NGFWs perform DPI, incorporate intrusion detection/prevention systems, URL filtering, and provide antivirus and antimalware functionality. They use artificial intelligence to detect threats that traditional firewalls might miss.
6. Filtering Internal and External Traffic
A perimeter firewall filters both internal and external traffic. Internal traffic refers to communications within the network, such as between users and internal devices, while external traffic originates from outside the network. External traffic poses greater risks due to numerous internet-based threats targeting the organization. The firewall examines each data packet for signs of malware or indicators of cybercriminal activity, ensuring strong protection against various cyber threats.
What are the Benefits of a Perimeter Firewall?

Perimeter firewalls are critical components of network security, offering numerous advantages such as managing traffic, mitigating attacks, and protecting data to ensure robust defense against cyber threats. Here are additional benefits of utilizing a perimeter firewall:
1. Network Performance
By preventing harmful or unnecessary traffic from congesting the network, perimeter firewalls help maintain optimal network performance. This allows legitimate network activities to proceed without interruption.
2. Compliance Support
By implementing security policies and documenting network traffic, perimeter firewalls help organizations comply with data protection regulations. This compliance is essential for adhering to legal requirements and industry standards.
3. Ensuring User Privacy
Perimeter firewalls act as intermediaries, enhancing user privacy by concealing internal network details from external entities. This protection ensures user information remains confidential.
4. Protection of Resources
These firewalls protect network resources by granting access only to verified users and services. This selective access prevents exploitation, unauthorized use, and potential downtime, ensuring the reliability and availability of network resources.
5. Data Breach Prevention
As the first line of defense against external threats, perimeter firewalls play a vital role in preventing data breaches. They protect sensitive information, which is crucial for maintaining organizational trust and confidentiality.
6. Visibility of Network Traffic
Perimeter firewalls provide visibility into all traffic entering and leaving the private network. This capability enhances corporate security and offers valuable insights into the usage of internal and external services, aiding better network management.
7. Filtering Malicious Content
NGFWs when deployed as perimeter firewalls, can identify and block malware and other malicious content from entering an organization’s network. This proactive filtering is essential for maintaining a secure digital environment.
8. Preventing Data Loss
Perimeter firewalls help prevent data loss by identifying and blocking traffic that does not comply with company policy. This function is crucial for protecting sensitive and valuable data from unauthorized access and exfiltration.
9. Management of Traffic
Perimeter firewalls control the flow of network traffic, permitting only data packets that are authorized to pass through. This control improves the security of the network by blocking unauthorized access and maintaining a strong security posture.
10. Attack Minimization
Serving as a crucial defense line, these firewalls defend against a range of cyber threats, such as intrusions and viruses. They block suspicious activities, reducing potential attacks before they have a chance to harm network integrity.
What are the Risks of a Perimeter Firewall?
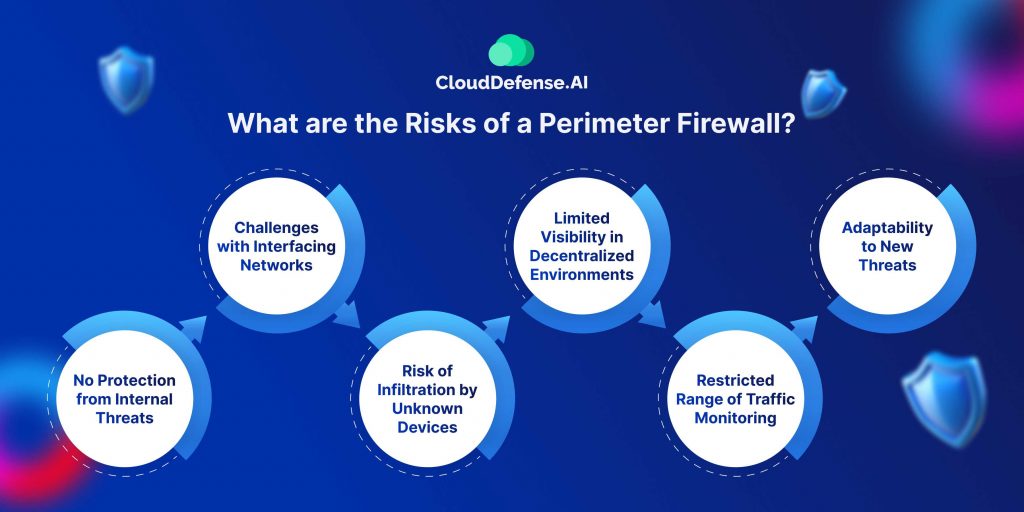
Even though perimeter firewalls offer significant benefits, they come with inherent risks. Understanding these limitations can help you develop a strong network security strategy.
1. No Protection from Internal Threats
Although perimeter firewalls are effective in defending against external threats, they do not inherently protect against internal risks like compromised internal systems or other malicious employees. This limitation highlights the need for additional security measures to protect against internal attacks.
2. Challenges with Interfacing Networks
When a company connects its network to another via the internet, it risks introducing malicious code or unauthorized individuals into its network. Additionally, perimeter firewalls may fail to detect insider attacks since the malicious data originates from within the network.
3. Risk of Infiltration by Unknown Devices
Perimeter firewalls can be infiltrated by unknown devices connecting from outside the network, such as employee laptops and mobile devices. Furthermore, businesses moving to the cloud must adapt their defenses to protect against attackers targeting cloud architectures, including data centers and SaaS providers.
4. Limited Visibility in Decentralized Environments
The increasing use of cloud services and decentralized architectures is expanding and obscuring the traditional boundaries of network perimeters. This change makes it hard for firewalls to offer complete protection, requiring the adoption of controls that operate in dispersed network environments.
5. Restricted Range of Traffic Monitoring
Perimeter firewalls primarily focus on monitoring incoming and outgoing traffic, often overlooking lateral traffic inside the network. This gap can enable internal threats to spread unnoticed, creating substantial security risks.
6. Adaptability to New Threats
Perimeter firewalls may have difficulty adapting to cyber threats. Innovative attack techniques, especially those directed at cloud services and complex systems, can occasionally evade conventional firewall protections, diminishing their overall effectiveness.
Perimeter Firewall vs. Client Firewall
Understanding the distinctions between perimeter and client firewalls can help you pick the right solution for your company. These two firewall types serve different roles in network security, providing unique protections for network boundaries and individual devices. Refer to the table below for a better understanding of each firewall type.
| Feature | Perimeter Firewall | Client Firewall |
| Location | Edge of the network | Individual devices or hosts |
| Scope of Protection | Entire network | Specific machines |
| Deployment | Centralized, managing all access points connecting to outer networks | Decentralized, installed on each device individually |
| Traffic Monitoring | Monitors all incoming and outgoing traffic at the network edge | Monitors exchange of data to and from the specific machine |
| Role | First line of defense against external threats | Provides localized protection, even outside the network perimeter |
| Management | Managed centrally by network administrators | Managed locally or by endpoint management systems |
| Protection Against | Unauthorized access, external threats | Internal and external threats specifically targeting the host device |
| Operational Continuity | Protects network infrastructure | Protects the device regardless of its location |
| Customization | Configured with network-wide policies | Configured with individual policies for each device |
| Visibility | Provides visibility into all traffic entering and leaving the network | Provides visibility into traffic specific to the protected device |
| Example Use Case | Blocking malicious content from entering the network | Preventing unauthorized applications from accessing the internet |
| Dependence on Network Position | Effective at the network’s edge | Effective regardless of network position |
Perimeter Firewall vs. Data Center Firewall
Perimeter and data center firewalls serve different security needs. Perimeter firewalls manage external traffic, while data center firewalls secure internal communications within dynamic virtualized environments. Let’s look at the key differences between these two.
| Feature | Perimeter Firewall | Data Center Firewall |
| Location | Network Boundary | Within the data center environment |
| Primary Function | Controls the access to resources on the network by monitoring/filtering external traffic | Security of the data center environment, managing internal (east-west) traffic |
| Traffic Management | Handles incoming and outgoing (north-south) traffic | Handles internal (east-west) traffic between virtual machines |
| Focus | Blocks access to any unauthorized visitors from outer sources | Provides granular control over internal data center traffic |
| Adaptability | Fixed rules for external threats | Flexibly adjusts to shifts within the data center environment, such as the migration of virtual machines. |
| Deployment | Deployed at the network perimeter | Deployed within the data center environment |
| Protection Against | External threats and attacks | Internal threats and traffic management within the data center |
| Operational Scope | Protects the entire network | Secures specific data center environments |
| Visibility | Provides visibility into all traffic going in and out of the network | Provides visibility into internal data center traffic |
| Example Use Case | Blocking malicious content from entering the network | Ensuring the security of inter-VM communications within the data center |
| Dependence on Network Position | Effective at the network’s edge | Effective within the data center, regardless of VM reconfigurations |
| Customization | Configured with network-wide policies | Configured with policies specific to data center operations |
| Resource Management | Protects network infrastructure | Protects and manages virtual resources within the data center |
Final Words
By now you know how a perimeter firewall helps protect a network from external threats by monitoring and filtering incoming and outgoing traffic. By defining the boundary between a private network and the public internet, perimeter firewalls provide the first defense against cyberattacks, malicious content, and unauthorized access. Implementing a perimeter firewall enhances security and optimizes network performance, ensuring that sensitive data remains protected against digital threats.







